A Quarter of All Hacked Sites may be Attributed to a few Plugins

A Quarter of All Hacked Sites may be Attributed to a few Plugins
Security firm Sucuri says that, throughout the primary 3 months of 2016, the corporate saw an outsized range of attacks targeting websites running on the WordPress CMS platform.
The company free yesterday its first-ever web site Hacked Report, during which it compiled statistics from over eleven,485 compromised sites it absolutely was known as upon to research.
As we tend to expect, an outsized portion of those compromised websites was running on WordPress, the foremost self-made CMS platform for the past five-six years.
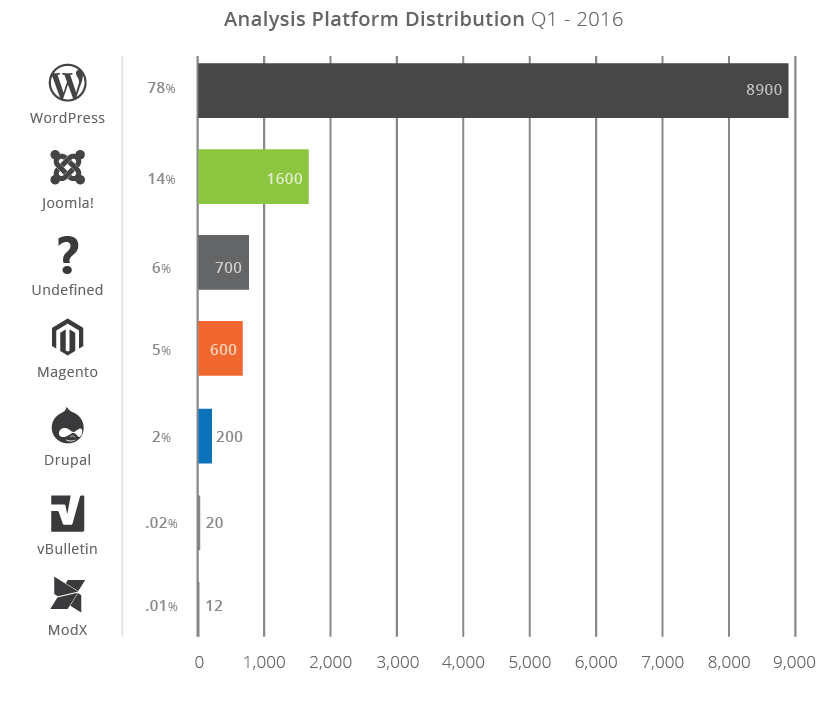
Nearly four in 5 hacked websites were running WordPress
More exactly, Sucuri reveals that seventy-eight p.c of the entire range of hacked websites it investigated were WordPress sites, with Joomla in a very distant second, seizing solely fourteen p.c of the information sample. Further, six p.c were no-CMS websites, five p.c were running Magento, and a pair of p.c were victimization Drupal.
Looking back at historical knowledge the corporate collected within the past years, Sucuri says that Q1 2016 was a quiet amount, with no visible spike within the range of infected websites in total, or for a precise platform.
Something like this happened last year, at the beginning of 2015, once the steal Magento bug was disclosed, and hackers tried to use it beginning day one.
It is owing to this same bug that Magento may be an extremely sought-out target, seeing additional attacks than Drupal, albeit there area unit additional Drupal sites online. In most cases, crooks United Nations agency hack Magento sites chase MasterCard numbers collected through payment pages and do not hassle with SEO spam or exploit kits, as is that the case with hacked WordPress, Joomla, and Drupal sites.
Point of entry for many hacks was a vulnerable plugin, not the CMS core
As for a breakdown of hacked WordPress sites, Sucuri says that an outsized half may be attributed to superannuated plugins. there have been smallest tries to use vulnerabilities within the WordPress core itself, and crooks relied on WordPress’ quality and its massive plugins and themes scheme to intercommunicate their injury.
Sucuri says that, from all the compromised WordPress sites they analyzed, they found the intrusion purpose within a vulnerable plugin. 1 / 4 of those attacks may be attributed to a few plugins: RevSlider, GravityForms, and TimThumb.
gotmls is additionally the plugin suspected to be at the core of the Panama Papers knowledge breach. What makes this datum additional mind-blowing is that the indisputable fact that, for all 3 plugins, developers free security fixes over a year agone. For TimThumb, the safety fix was free four years agone, nevertheless there area unit still WordPress sites victimization the plugin’s vulnerable version.
This is as a result of, like goals, there area unit plenty of developers that have embedded these plugins within custom themes, sometimes business products offered through theme marketplaces like ThemeForest, magic Themes, and others.
Even if plugins may be deployed mechanically with themes throughout the theme’s installation, theme developers have chosen to insert plugins inside the theme’s code soon permit users to manage their content via a central theme board.
This kind of setup makes upgrading the plugin’s code via the WordPress integral plugin manager not possible, and theme developers ought to re-issue themes with new plugin versions once every few months. Which, as you guessed it, most don’t.
WordPress is really adding up thus far compared to different CMSs
While this follow has died down, it existed for several years, which explains the massive range of vulnerable WordPress websites that cannot be updated with ease.
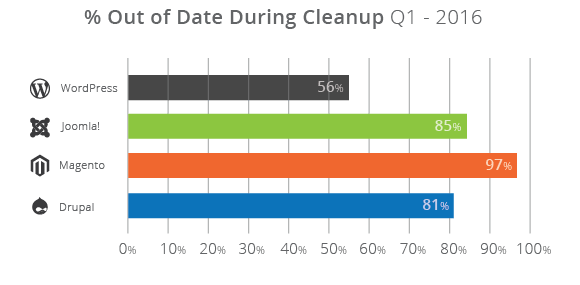
In fact, Sucuri says that, despite the grim state of affairs, WordPress is really in a very smart position. the safety firm says that, out of all the compromised websites, solely fifty-six p.c of WordPress sites were running superannuated WordPress core versions.
For Joomla, this range was eighty-five p.c, for Drupal it absolutely was eighty-one p.c, whereas for Magento, wherever the upgrade method may be a pain in “you grasp wherever,” this was ninety-seven p.c.
“These statistics sit down with the challenges web site homeowners face, despite the size, business, or trade. web site homeowners area unit unable to stay up with the rising threats. As well, the steering they receive to ‘stay current’ or ‘just update’ isn’t enough,” Sucuri explained. “Website homeowners area unit turning to different technologies, like web site Application Firewall (WAF), to offer themselves and their organizations the time they need to add with efficiency reply to the threats by a method of virtual repair and hardening techniques at the sting.”
